Three foundational decisions have been formalized in this version. We are transparent about what changed, why we made these choices, and why we believe this version of XInfinitum represents a superior, more trustworthy, and more durable network design.
1. Mandatory KYC for all wallet creation. Every wallet address issued on the XInfinitum network requires verified identity before activation. Your identity is never public, never stored by Pilon Laboratories, and only accessible through DAO-governed legal process — exactly as your bank account works. This eliminates anonymous-wallet-dependent crime at the protocol level. See Section 6.
2. PQC-only bridge policy. Only assets secured by post-quantum cryptography may bridge natively to the XInfinitum network. Classical-cryptography assets (BTC, ETH in their current form) use ECDSA custody wallets — which Shor's algorithm can break. Allowing them to bridge would introduce the exact quantum vulnerability XInfinitum was built to eliminate. A network is only as strong as its weakest link. See Section 6.4.
3. Roadmap revised to reflect realistic timelines. Planned Testnet: Q2 2027. Planned Mainnet: Q1 2028. Building the most secure blockchain infrastructure ever created takes time we are not willing to compromise on. We believe the community will understand and appreciate this candour. See Section 14.
Abstract

"XInfinitum" — Without end, without limit. A network whose keys are born from quantum infinity and vanish just as fast.
Every transaction signed by a key that has never existed before and will never exist again.
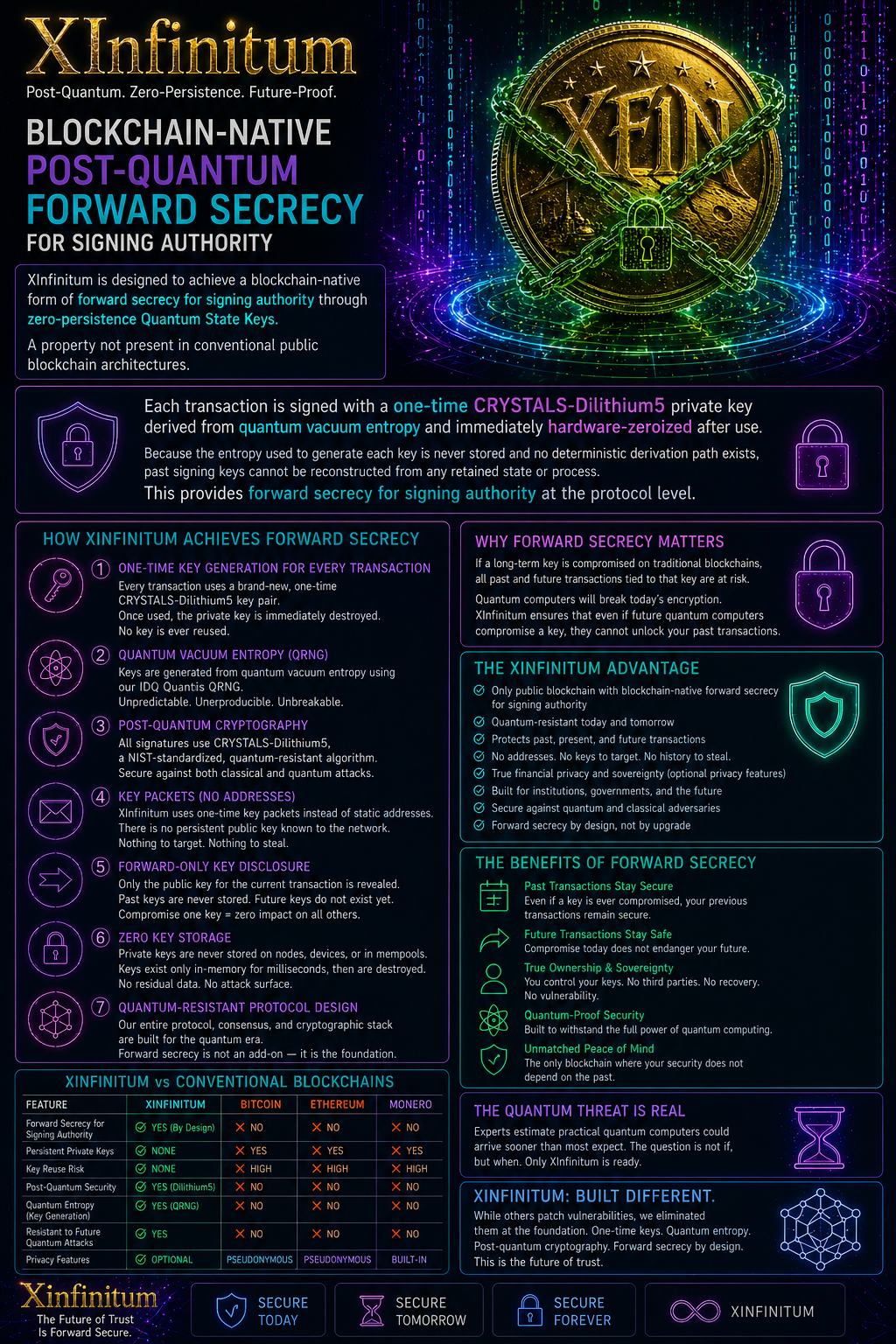
XInfinitum is a novel Layer 1 blockchain that combines AI-driven consensus, zero-knowledge machine learning (zkML) proofs, quantum-derived transaction keys, and post-quantum encrypted token storage to produce a network that is simultaneously transparent in its decision-making, accountable in its transaction history, and the most secure signing infrastructure ever built for a public blockchain.
The XInfinitum network replaces traditional Proof-of-Stake validators with a diverse ecosystem of staked AI agent validators, each running distinct proprietary models. These agents reach Byzantine Fault Tolerant (BFT) consensus on block validity and publish cryptographic proofs of every decision to a public proof ledger — making the consensus process independently verifiable by anyone, anywhere, without revealing the AI models themselves.
Every wallet address on XInfinitum belongs to a verified unique human being. Identity is confirmed once at onboarding through a zero-knowledge KYC process — your legal identity is never public, never stored after verification, and only accessible through DAO-governed legal process. Wallet addresses are private (not publicly broadcast) and known only to counterparties you transact with. This is financial accountability without surveillance: the same model as your bank account, with far stronger cryptographic privacy guarantees. No classical encryption is permitted anywhere on the XInfinitum network — every component, from transaction signatures to bridge custody, uses NIST-standardized post-quantum cryptography.
Most distinctively, XInfinitum introduces Quantum State Keys — wallet signing keys that do not exist in persistent storage. Derived from quantum random number generation at the exact moment of signing and immediately discarded thereafter, Quantum State Keys make it cryptographically impossible to steal a private key that never persisted long enough to be stolen.
1 · The Problem
1.1 The Validator Trust Problem
Proof-of-Stake consensus relies on economic incentives to align validator behavior with network interests. This model carries structural weaknesses:
- Software homogeneity: Most validators run identical client software. A single zero-day exploit can cascade across the entire validator set simultaneously.
- Validator concentration: The largest stakers exert disproportionate influence over both consensus and governance.
- No active intelligence: Deterministic validators check whether transactions follow rules but cannot detect novel attack patterns, flash loan attacks in formation, or emerging threats before they execute.
- Opaque decision-making: There is no public record of how a validator reached its decision — only what was decided.
1.2 The Key Storage Problem
Every classical wallet — software, hardware, paper — stores a static private key. This key signs every transaction the wallet ever makes. A single breach exposes the wallet's entire history and all future funds permanently. There is no forward secrecy and no recovery.
1.3 The Quantum Threat
Current blockchain cryptography (ECDSA, secp256k1) is vulnerable to Shor's algorithm on a sufficiently powerful quantum computer. The threat of harvest now, decrypt later attacks is immediate — adversaries can collect blockchain data today and decrypt it retroactively once quantum hardware matures. Any blockchain launched today with classical cryptography will have its entire transaction history exposed within a generation.
1.4 The Verifiability Gap
No existing system achieves: verifiable, provable decision-making at the consensus layer; quantum-resistant signing at the wallet layer; and user-controlled privacy at the transaction layer — simultaneously. XInfinitum is built to close this gap entirely.
2 · Vision & Design Philosophy
XInfinitum is built on five foundational principles:
Every wallet on XInfinitum belongs to a verified unique human being. Identity is confirmed once at onboarding — your legal identity is never public, never stored by Pilon Laboratories, and only accessible through DAO-governed legal process. This is identical to how your bank account works: fully accountable to law where law demands it, fully private from everyone else. Anonymous wallets are not a privacy tool — they are a crime tool. XInfinitum eliminates one while fully protecting the other. A network is only as strong as its weakest link; one anonymous wallet is enough to attract bad actors who poison the entire ecosystem.
Anyone must be able to verify that the network is functioning correctly without being able to see transaction details, validator model internals, or user identities. Zero-knowledge proofs make this possible.
Post-quantum cryptography is not an upgrade XInfinitum will apply later. It is foundational from genesis block. No transaction on XInfinitum will ever be vulnerable to future quantum decryption, including harvest-now-decrypt-later attacks.
Rule-based validation is a solved problem. XInfinitum consensus adds active intelligence: anomaly detection, attack pattern recognition, cross-chain threat correlation, and real-time adaptive response.
A private key that never persists cannot be compromised. Quantum State Keys exist only at the quantum moment of signing — generated, used, and destroyed in a single atomic operation leaving no recoverable trace.
3 · Architecture Overview
XInfinitum is a Layer 1 blockchain. It does not inherit security, consensus, or data availability from any other network. Every component operates at the base protocol layer.
3.1 Node Types
Four distinct node roles exist on the XInfinitum network. Each has different hardware requirements, staking obligations, and responsibilities.
| Node Type | Role | Staking Required | GPU Required | Who Runs It |
|---|---|---|---|---|
| Validator Node | Runs AI model · Generates zkML proofs · Participates in BFT consensus · Votes on blocks | Yes — $33,333 USD equiv. minimum | Yes — A100-class or equivalent | DAO-approved AI operators |
| Storage Node | Stores encrypted XFIN token shards · Serves shard retrieval · Distributes decoy shards | Yes — 5,000 XFIN minimum | No | Individuals or organisations with storage infrastructure |
| Full Node | Validates all blocks independently · Serves RPC to applications · Maintains full chain history | No | No | Developers · dApp operators · exchanges · researchers |
| Light Client | Verifies block headers only · Uses Merkle proofs for transaction inclusion · Suitable for mobile wallets | No | No | End-user mobile and desktop wallets |
4 · AI Consensus Layer
XInfinitum replaces homogeneous software validators with a diverse ecosystem of staked AI agent validators. Traditional PoS achieves economic alignment through staking but fails at behavioral diversity — all validators run nearly identical software and fail in identical ways. XInfinitum achieves both: economic alignment through mandatory staking with slashing, and behavioral diversity through the requirement that each validator run an architecturally distinct, proprietary model.
4.1 Validator Requirements
| Requirement | Specification |
|---|---|
| Minimum stake | $33,333 USD equivalent in XFIN — maintained continuously at all times |
| Stake floor enforcement | Automatic suspension if stake drops below USD floor; validator must top up within 72 hours or be deactivated |
| Initial lock period | 1 year minimum from activation date |
| Model uniqueness | Architecture must be demonstrably distinct via zkML model commitment hash |
| Model type | Proprietary closed-source weights required |
| Uptime SLA | ≥ 99.5% over any 30-day period |
| Response latency | Median block validation ≤ 500ms |
| Proof submission | zkML proof submitted with every validation vote |
| DAO approval | New validators approved by DAO governance vote |
4.1.1 Validator Staking Rewards
Validator staking rewards (25–40% APY on staked position) are owned entirely by the validator. They serve three practical functions:
- Compute cost coverage: Running a proprietary AI model at 99.5% uptime with ≤500ms response latency requires significant compute infrastructure. Rewards are sized to cover these costs at healthy margins.
- Slashing risk premium: Validators put capital at risk. Rewards compensate for this exposure.
- Profit and reinvestment: Any surplus beyond costs is the validator's to keep, withdraw, or compound back into their staked position.
Validator rewards are paid from the network fee pool (50% of all network fees) and are entirely separate from the Praemium surplus. The two pools cannot cannibalize each other by design.
4.1.2 XInfinitum Validator Bootstrap Grant Program
The $33,333 USD staking requirement is intentionally set at a level that aligns validator economics with network success — but the XInfinitum Foundation recognizes that talented AI researchers and independent model developers may not have this capital available at the time of application. The Validator Bootstrap Grant Program addresses this directly.
Qualifying validator applicants may apply to the XInfinitum Foundation DAO for a grant covering all or part of their initial staking requirement. Grants are funded from the Foundation Treasury allocation and governed by DAO vote. The program operates as follows:
- Eligibility: Applicant must pass DAO technical review — demonstrating a genuinely distinct, functional AI model with a verified zkML commitment hash.
- Grant structure: Up to $33,333 USD equivalent in XFIN provided as a staking grant. The XFIN is staked directly to the validator's position on activation — it is not paid as cash.
- Repayment: A fixed percentage of the validator's earned rewards (governed by DAO, typically 20–30%) is automatically withheld and returned to the Treasury until the full grant amount is repaid.
- Exit before repayment: If a validator exits or is slashed before full repayment, the outstanding balance is recovered from their staked position before any remainder is returned to the validator.
- Full ownership on repayment: Once the grant is fully repaid, the validator retains 100% of all future rewards with no further obligation to the Foundation.
4.2 Byzantine Fault Tolerance
XInfinitum uses a Tendermint-derived BFT consensus adapted for AI validators. The network tolerates up to f Byzantine validators where f < n/3:
| Phase | Validators | Byzantine Tolerance |
|---|---|---|
| Testnet launch | 7 validators | 2 Byzantine |
| Mainnet genesis | 15 validators | 4 Byzantine |
| Growth target | 51 validators | 16 Byzantine |
| Mature network | 100+ validators | 33+ Byzantine |
Because validators run architecturally different models, a successful coordinated attack requires simultaneously compromising distinct AI systems across different organizations — exponentially more difficult than attacking homogeneous software.
4.3 Anomaly Detection & Real-Time Response
Each validator runs a dedicated anomaly detection module monitoring mempool patterns, cross-block analysis, network behavior, smart contract behavior, and cross-chain signals. Anomaly severity is scored 0.0–1.0 with automated escalation:
| Severity | Score Range | Automated Response |
|---|---|---|
| Low | 0.85 – 0.92 | Flag transaction, defer to next block, log publicly |
| Medium | 0.92 – 0.97 | Pause transaction, require 2/3 validator quorum, DAO notified |
| High | 0.97 – 1.0 | Network-wide alert, temporary mempool freeze, DAO emergency session triggered |
4.4 Block Time, TPS & Finality
XInfinitum targets a 2-second block time using its Tendermint-derived BFT consensus. BFT consensus provides single-block finality — a transaction included in a finalised block is mathematically irreversible with no waiting for confirmations. There are no reorgs on XInfinitum.
| Metric | Value | Notes |
|---|---|---|
| Target block time | 2 seconds | Consistent across all validator set sizes |
| Finality type | Instant (BFT) | One block = final. No probabilistic confirmation waiting. |
| Finality time | ~2 seconds | Transaction is irreversibly settled at block inclusion |
| Block size target | 128 MB | Required to accommodate CRYSTALS-Dilithium5 signature sizes — see §7.6 |
4.4.1 TPS by Validator Set Size
Throughput scales with block size and transaction processing capacity. BFT message complexity is O(n²) in validator count, meaning larger validator sets exchange more consensus messages per block — this is a modest overhead at the validator counts XInfinitum targets, and is offset by behavioural diversity gains at each tier.
| Phase | Validators | Base Layer TPS | With L2 (Phase 4) |
|---|---|---|---|
| Testnet | 7 | ~5,000 TPS | — |
| Mainnet genesis | 15 | ~4,000 TPS | — |
| Growth | 51 | ~3,000 TPS | ~500,000+ effective TPS |
| Mature network | 100+ | ~2,000 TPS | ~1,000,000+ effective TPS |
4.4.2 Competitive Throughput Comparison
| Network | TPS | Finality | Post-Quantum |
|---|---|---|---|
| Bitcoin | ~7 | 60+ min (probabilistic) | No |
| Ethereum | ~15–25 | ~12 min (soft) / 15 min | No |
| Solana | ~65,000 | ~0.4s (optimistic) | No |
| Visa network | ~24,000 avg | Immediate (centralised) | N/A |
| XInfinitum (mainnet) | ~4,000 TPS | ~2s (BFT — mathematical) | Yes — NIST Level 5 |
4.5 zkML Proof Timing Architecture
A question arises naturally: if zkML proof generation targets under 30 seconds (GPU-accelerated), and block time is 2 seconds, how are proofs submitted with every validation vote?
The answer is pipeline parallelism. Validators use a two-stage overlapping pipeline:
This means proofs always lag exactly one block behind the vote they prove. The proof for Block N's decision arrives with the vote for Block N+1 (~2 seconds later). Proof verification takes ~2ms on any standard node and happens asynchronously — it does not stall consensus. The Public Proof Ledger records votes immediately and marks proofs as pending until submission, then verified.
4.6 Slashing Conditions
Slashing is the protocol's enforcement mechanism for validator misbehaviour. All slashable conditions and their consequences are defined at the protocol level and enforced automatically by the network — no DAO vote is required for a slash to execute. Slashed stake is split: 50% permanently burned (contributing to XFIN deflationary pressure) and 50% redirected to the Praemium surplus pool (benefiting all verified humans on the network).
| Offence | Slash | Additional Penalty | Description |
|---|---|---|---|
| Double-signing | 10% of stake | Permanent jail — DAO vote required for reinstatement | Signing two conflicting blocks at the same height. Cryptographic proof submitted by any node. Most severe — indicates deliberate attack or critical failure. |
| Invalid zkML proof | 3% of stake | 48-hour suspension · Automatic resume after | Submitting a zkML proof that fails on-chain verification — proof does not correspond to the validator's committed model hash. |
| Model hash mismatch | 15% of stake | Mandatory DAO review before reinstatement | Detected change in AI model weights without a prior DAO-approved model commitment update. Indicates potential model swap attack. |
| Proof delinquency | 1% of stake | 48-hour suspension | Three consecutive missed zkML proof submissions within a 24-hour period. |
| Uptime SLA breach | 1% of stake | 72-hour suspension | Uptime below 99.5% in any 30-day rolling window. Measured by missed block votes. |
| Stake floor breach | None | Automatic deactivation after 72-hour cure period | Stake drops below the USD-equivalent floor. No slash — validator is suspended until top-up is confirmed. No slashing for market price movements. |
4.7 Validator Hardware Requirements
Validators must sustain ≤500ms median block validation latency and generate PLONK zkML proofs in under 30 seconds at 99.5% uptime. This requires dedicated infrastructure — not a consumer desktop. The following represents minimum and recommended specifications.
| Component | Minimum | Recommended | Why |
|---|---|---|---|
| GPU | NVIDIA A100 40GB or RTX 4090 | NVIDIA H100 80GB or dual A100 | zkML PLONK proof generation <30s requirement — GPU VRAM is the bottleneck for large model proofs |
| System RAM | 64 GB ECC | 256 GB ECC | AI model loading + mempool processing + chain state |
| Storage | 4 TB NVMe SSD | 8 TB NVMe RAID-1 | Full chain history + zkML proof archive + model weights |
| CPU | 32-core server CPU | 64-core server CPU (AMD EPYC / Intel Xeon) | Parallel transaction validation + BFT message handling |
| Network | 1 Gbps symmetric dedicated | 10 Gbps symmetric dedicated | 128 MB blocks at 2s intervals = sustained ~512 Mbps raw throughput requirement at peak |
| Uptime infrastructure | UPS + redundant ISP | Colocation data centre (Tier 3+) | 99.5% uptime SLA — single ISP failure causes slashing |
5 · zkML Proof System
For every block validation vote, each XInfinitum AI validator generates a zero-knowledge machine learning proof asserting that it possessed its DAO-approved model, ran the block data through it, and produced the stated validation decision — without revealing the model's weights, internal computation, or any other data.
5.1 Proof System: PLONK
| Parameter | Specification |
|---|---|
| Proof generation time | Target < 30 seconds (GPU-accelerated) |
| Proof size | ~500 bytes |
| Verification time | ~2ms on any standard node |
| Model commitment | SHA3-256(architecture_spec ‖ weight_merkle_root ‖ version ‖ timestamp) |
5.2 The Public Proof Ledger
Every block includes a complete consensus record published to the Public Proof Ledger: every validator's vote, every zkML proof hash, every anomaly flag, and every resolution. This is unprecedented transparency in blockchain consensus — XInfinitum proves not just that consensus was reached, but how it was reached, mathematically, publicly, permanently.
6 · Identity & Compliance Layer
6.1 Why We Made This Decision
XInfinitum was designed from genesis block to be the financial infrastructure of the next era — not a tool for the last era's crime wave. In the history of cryptocurrency, anonymous wallets have enabled ransomware that shut down hospitals, trafficking payments, terrorism financing, and exchange frauds that cost ordinary people billions. These are not edge cases — they are the primary use case of anonymous crypto in practice, and every legitimate user pays the price through regulatory crackdowns, exchange delistings, and industry-wide reputational damage.
The decision is simple: a network is only as strong as its weakest link. If one wallet in a thousand is anonymous, that wallet becomes the preferred attack vector for every criminal operating on the platform. The anonymous minority destroys the environment for the compliant majority. XInfinitum eliminates this tradeoff entirely. Every participant is a verified unique human being. No exceptions. No dark corners.
We hope the community understands and embraces this decision. The people who built wealth on Bitcoin and Ethereum — the legitimate majority — were never served by anonymity. They were hurt by it. The regulatory pressure, the exchange delistings, the banking refusals, the tainted-coin blacklists — all of it traces back to the same root cause: anonymous wallets made crypto a preferred tool for financial crime, and the industry as a whole paid the price. XInfinitum was designed from the first line of code to be the network where that story ends.
| Crime Type | Why It Requires Anonymity | What Changes on XInfinitum |
|---|---|---|
| Ransomware payments | Attacker needs untraceable receive wallet | Every receive wallet is a verified identity. First payment = immediate law enforcement identification. |
| Money laundering | Requires anonymous layering and tumbling across multiple addresses | Every address is a real person. No layering possible. Every hop is traceable to a verified individual. |
| Terrorism financing | Funding flows must be untraceable to source | Every funding source is an identified person. Wire transfer to an anonymous crypto address is impossible. |
| Sanctions evasion | Sanctioned entities need wallets that don't reveal their identity | Wallet issuance is identity-verified. Sanctioned individuals and entities cannot receive wallet addresses. |
| Rug pulls / exit scams | Project founders need untraceable withdrawal addresses | Every founder, developer, and project wallet is KYC'd. Identity is on-chain. Fraud is legally actionable from day one. |
| Market manipulation | Wash trading requires thousands of fake wallet addresses | Each wallet is a real, unique verified human. Creating fake volume requires real identities — impossible at scale. |
| Darknet commerce | Buyers and sellers need mutual anonymity | Every buyer and seller is a verified person. Pseudonymous darknet commerce cannot function. |
| Exchange fraud | Fraudulent accounts require anonymous wallets | One wallet per verified human. Account farming and sybil attacks are structurally eliminated. |
6.2 What KYC Means for Legitimate Users
- No regulatory risk: Your transactions are architecturally compliant. No retroactive exchange delisting, no "tainted coin" blacklisting, no surprise regulatory action against your holdings.
- Institutional access: Pension funds, family offices, endowments, and regulated financial institutions can hold XFIN without legal compliance concerns. The institutional capital that has been blocked from pseudonymous crypto is now accessible.
- Insurance eligibility: Financial regulators and insurers can cover XFIN holdings. Insured crypto custody becomes a standard offering, not an exception.
- Banking relationships: KYC-compliant networks can maintain banking partnerships that pseudonymous chains cannot. Fiat on/off ramps are simpler, cheaper, and more reliable.
- Exchange listings: Regulated exchanges (Coinbase, Kraken, Binance) are under FATF Travel Rule compliance requirements. XInfinitum's built-in KYC model may make it the most exchange-friendly Layer 1 ever launched.
- Card program access: The XInfinitum Card Program integrates seamlessly because the KYC is already done. No separate onboarding for spending functionality.
- You already KYC everywhere that matters: Your bank, your brokerage, your phone carrier, your exchange. The only places that don't require it are the ones that attract fraud.
6.3 KYC Onboarding Flow — Step by Step
Wallet creation takes approximately 5–10 minutes for most applicants. No biometric data, identity documents, or personally identifiable information is ever stored by Pilon Laboratories — all verification is processed by our ZK-KYC partner with immediate deletion after proof generation.
| Step | Action | What Happens to Your Data |
|---|---|---|
| 1 — Download & Begin | Download PALLAS Wallet App or visit the onboarding portal | No data collected yet |
| 2 — Government ID | Present passport, driver's licence, or national ID card | Document processed once · Permanently deleted after verification · Only cryptographic hash of verification event retained |
| 3 — Biometric Liveness | Live face scan or fingerprint confirms real human (not photo, video, or AI) | Hardware liveness detection (PALLAS device) or phone TEE · Biometric data never leaves device or is deleted immediately after liveness confirmation |
| 4 — ZK Identity Proof | Zero-Knowledge Enrollment Proof generated | Proof asserts only "unique verified human" — reveals nothing else · Non-reversible nullifier stored on-chain to prevent duplicate enrollment · Your identity is gone from our systems |
| 5 — Wallet Created | Address derived from ZK proof + fresh quantum entropy | Address is private — not publicly broadcast · Known only to you and counterparties you transact with |
| 6 — .xfin Username | Optional human-readable address (e.g. derek.xfin) | Not publicly discoverable · No link between username and legal identity is ever published |
| ✓ Activated | Full network access granted | Send/receive · Staking · Praemium enrollment · DAO governance · Card program |
6.4 PQC Bridge Policy — A Network Is Only As Strong As Its Weakest Link
XInfinitum is the most quantum-secure blockchain ever built. But a network's security ceiling is set by its weakest component. If XInfinitum were to allow BTC or ETH to bridge in via a custody wallet — that custody wallet uses ECDSA. ECDSA is fully broken by Shor's algorithm. A sufficiently powerful quantum computer could drain every satoshi and every ether in that bridge custody wallet in a single attack. The ECDSA-locked bridge becomes a massive target with a known mathematical vulnerability — the single weakest link that invalidates everything else XInfinitum was built to protect.
| Bridge Requirement | Specification |
|---|---|
| Source chain consensus | Must use PQC signatures (CRYSTALS-Dilithium5 or equivalent NIST FIPS 204 standard) |
| Bridge custody wallet | Must use PQC key management — no ECDSA, no secp256k1, no RSA |
| Bridge protocol encryption | All protocol communications must use NIST-approved PQC key exchange — no TLS with ECDH |
| Bridge approval | Every new bridge must pass DAO security review and governance vote before activation |
| Classical assets (BTC, ETH) | Not eligible for native bridge in current form. Fiat on-ramp → XFIN purchase is the path. Bridge eligibility conditional on source chain PQC upgrade. |
6.6 Regulatory & Compliance Framework
XInfinitum's mandatory KYC architecture makes it the first Layer 1 blockchain that is structurally compliant with global AML/CFT frameworks by design — not as an afterthought. This section outlines how the protocol maps to current regulatory requirements and XInfinitum's approach to operating within them.
6.6.1 FATF Travel Rule Compliance
The Financial Action Task Force (FATF) Travel Rule (Recommendation 16) requires Virtual Asset Service Providers (VASPs) to collect, retain, and transmit originator and beneficiary information for transactions above $1,000 USD. XInfinitum is structurally compliant with this requirement: because every wallet address is bound to a verified unique identity through the ZK-KYC enrollment process, the originator and beneficiary of every transaction are already cryptographically identified. Compliance is architectural, not procedural — no separate Travel Rule data collection layer is required on top of the base protocol.
6.6.2 Canadian Regulatory Status
Pilon Laboratories Inc. is a Canadian corporation incorporated in Nova Scotia. Prior to mainnet launch, Pilon Laboratories will:
- Register as a Money Services Business (MSB) with FINTRAC (Financial Transactions and Reports Analysis Centre of Canada) — required for any Canadian entity engaged in virtual currency exchange or transfer
- Engage in pre-consultation with the Ontario Securities Commission (OSC) and applicable provincial securities regulators regarding the XFIN token classification
- Incorporate the XInfinitum Foundation in the Cayman Islands as the non-profit DAO legal entity responsible for protocol governance
- Engage Canadian legal counsel specialising in fintech and digital assets to ensure full compliance at mainnet launch
6.6.3 Jurisdiction Restrictions at Launch
Wallet issuance and XFIN token access will be restricted at launch for individuals and entities in the following categories:
| Restriction Category | Basis |
|---|---|
| OFAC Specially Designated Nationals (SDN List) | US sanctions law — no XFIN wallet issuance, no transactions |
| FATF High-Risk Jurisdictions (Blacklist) | Currently: North Korea, Iran, Myanmar — subject to update as FATF list evolves |
| UN Security Council Sanctioned Entities | International sanctions compliance |
| Jurisdictions with explicit crypto bans | Determined on a per-jurisdiction basis pre-launch; DAO may expand or contract this list through governance |
Jurisdiction restrictions are enforced at the KYC onboarding layer — restricted individuals cannot complete the ZK-KYC enrollment and therefore cannot receive a wallet address. This is structurally enforced, not policy-only.
6.6.4 Identity Registry Legal Structure
The DAO-governed identity registry is the most legally sensitive component of the XInfinitum architecture. Its governance structure is designed to balance privacy protection with lawful legal process:
- Legal custodian: The XInfinitum Foundation (Cayman Islands) holds legal responsibility for the identity registry as a non-profit foundation with a defined public benefit mission
- Access threshold: Identity disclosure requires a formal court order from a recognised jurisdiction — not a law enforcement request, a regulatory inquiry, or a VASP-to-VASP information share. Court orders only.
- DAO veto right: The DAO governance layer has the right to contest identity disclosure requests through the Foundation's legal counsel before compliance — providing an additional layer of procedural protection for users in jurisdictions with weak rule of law
- Minimal data held: The registry holds only the non-reversible ZK nullifier tied to the verified identity event — not the identity document itself, not biometric data, and not the wallet address in plaintext. Identity recovery from the registry requires re-KYC with the original document.
6.5 No Classical Encryption on the XInfinitum Network
XInfinitum enforces a complete post-quantum cryptography requirement across every network component. Classical encryption algorithms (ECDSA, RSA, Diffie-Hellman, secp256k1) are not supported anywhere on the network, at any layer, under any circumstances. This is not a roadmap item — it has been the architectural requirement since genesis block design.
| Network Function | Classical Equivalent (Banned) | XInfinitum Standard |
|---|---|---|
| Transaction signatures | ECDSA / secp256k1 | CRYSTALS-Dilithium5 (NIST FIPS 204 · Level 5) |
| Key exchange / encapsulation | Diffie-Hellman / ECDH | CRYSTALS-Kyber (NIST FIPS 203) |
| Token storage encryption | RSA encryption | CRYSTALS-Kyber + AES-256-GCM |
| P2P network encryption | TLS with ECDH cipher suites | PQC key exchange + CRYSTALS-Dilithium5 auth |
| Validator communications | Classical TLS / ECDSA certs | All PQC-secured — no classical cipher suites |
| Smart contract signatures | ECDSA-compatible contract addresses | CRYSTALS-Dilithium5 — no ECDSA contract keys |
| Bridge custody wallets | ECDSA custody locks | PQC wallets only — no ECDSA bridge locks permitted |
| Identity registry | Classical PKI / RSA certificates | PQC-secured ZK proof verification |
7 · Quantum State Keys
Every private key ever generated for any classical wallet shares one fatal property: it was stored somewhere. Storage is exposure risk. A key that exists can be found. Quantum State Keys do not exist until the moment they are needed.
7.1 Security Properties
| Property | Guarantee |
|---|---|
| Pre-existence | Does not exist before the moment of transaction signing |
| Entropy source | Generated from quantum measurement — true randomness, not algorithmic |
| Transaction binding | Derived to be specific to exactly one transaction |
| Destruction | Immediately and permanently destroyed after signing |
| Ownership proof | ZK proof proves wallet ownership without revealing key derivation path |
| Traceability | Leaves no recoverable trace in any storage medium |
| Uniqueness | Different for every transaction — no two are ever alike |
| Non-reproducibility | Cannot be predicted, reconstructed, or reverse-engineered |
7.2 Protocol — Transaction Signing
7.3 Attack Resistance Matrix
| Attack Vector | Classical Hardware Wallet | Quantum State Key |
|---|---|---|
| Device theft | Full historical compromise | No past keys recoverable — destroyed at use |
| Memory forensics | Key may be extractable | Key existed for microseconds — forensically irrecoverable |
| Malware / keylogger | Key captured at use | Key exists for < 1ms — no logging surface |
| Supply chain compromise | Persistent key exposed | No persistent key to expose |
| Quantum computer (Shor) | ECDSA fully broken | CRYSTALS-Dilithium5 is quantum-resistant (NIST Level 5) |
| Database breach | Stored keys compromised | Nothing to breach — no key database |
| Harvest-now-decrypt-later | All past transactions exposed | Nothing to harvest — key never existed in ciphertext |
7.4 Perfect Forward Secrecy — Transaction Level
XInfinitum is designed to be the first public blockchain to achieve post-quantum forward secrecy for signing authority at the individual transaction granularity — a security property stronger than anything offered by existing blockchains, messaging protocols, or financial systems. Understanding why this matters requires understanding what this means, what it protects against, and why no other blockchain has been designed to provide it.
What Perfect Forward Secrecy Means
Perfect Forward Secrecy is a guarantee about your history. It answers the question: "If an adversary compromises something today, can they reach backward and expose what I did before?"
On Bitcoin, Ethereum, Solana, and every other major blockchain today, the answer is yes. Each wallet has one keypair that signs every transaction it ever makes. That single key protects your entire transaction history — past, present, and future. If that key is ever compromised through theft, forensic analysis, a hardware vulnerability, or a future quantum computer using Shor's algorithm — every transaction you have ever made is exposed simultaneously.
Nation-state intelligence agencies are already exploiting this through harvest now, decrypt later strategy: recording blockchain data and signed transactions today, then waiting until quantum computers powerful enough to break ECDSA become available. Every Bitcoin and Ethereum transaction ever broadcast is potentially sitting in an archive, waiting for the decryption technology to arrive. When it does, pseudonymous identities will be linked, wallet histories fully exposed, and the assumption of financial privacy retroactively shattered.
XInfinitum's Quantum State Keys eliminate this attack surface completely. Because every transaction is signed by a key that is generated and destroyed within the same atomic operation, there is no key to harvest, no archive to decrypt, and no historical exposure to worry about — ever.
Why Other Blockchains Cannot Offer This
Perfect Forward Secrecy requires three things that no other blockchain has simultaneously built into its design:
- A different key per transaction: Using a different signing key for every transaction means no single compromise exposes multiple transactions. Classical blockchains use one keypair forever, by design — changing this would break wallet address continuity and the entire UTXO/account model.
- True random entropy per signing event: The per-transaction key must be derived from entropy that did not exist before the transaction and cannot be reproduced. Algorithmic pseudorandomness (PRNG) fails this test — a seed can be recorded or predicted. Hardware QRNG from genuine quantum physical measurements satisfies this requirement; software systems cannot.
- Verified hardware destruction: The ephemeral private key must be confirmed gone by hardware, not merely deleted by software. Software deletion leaves memory residue recoverable by forensic tools. Only a secure element with hardware-enforced zeroization and destruction verification closes this gap.
XInfinitum is the only blockchain designed from genesis with all three properties: every transaction uses a unique Quantum State Key (requirement 1), seeded by a hardware QRNG at the moment of signing (requirement 2), and the key is cryptographically zeroized inside the EAL6+ SLE97 Secure Element and confirmed destroyed by the PALLAS device's independent MCU (requirement 3). The math checks out, the hardware enforces it, and the certification validates it.
| Property | Bitcoin / Ethereum | Messaging (TLS 1.3) | XInfinitum QSK |
|---|---|---|---|
| Keys per session/transaction | One key — forever | Ephemeral per session | Ephemeral per transaction |
| Entropy source | Software PRNG / seed phrase | OS CSPRNG | Hardware QRNG — quantum vacuum |
| Key destruction | Never — key persists indefinitely | Software — OS managed | Hardware zeroization · SLE97 EAL6+ · MCU-verified |
| Quantum-resistant signature | No — ECDSA breakable by Shor | Partially (depends on suite) | Yes — CRYSTALS-Dilithium5 (NIST Level 5) |
| Forward secrecy scope | None | Session-level | Per-transaction — maximum granularity |
| Historical exposure on compromise | All past & future transactions | Prior sessions safe (computational) | Zero — past keys do not exist |
| Harvest-now-decrypt-later resilient | No | Partially (session keys ephemeral) | Yes — no key material ever persists in any form |
What This Means for XInfinitum Users
For every person who transacts on XInfinitum, Perfect Forward Secrecy provides a form of peace of mind that has never existed in cryptocurrency before:
- Your transaction history is permanently yours, locked by keys that no longer exist. No adversary — regardless of future computing power — can go backward through your XInfinitum history, because the keys that signed your past transactions are gone from the universe.
- A lost or stolen PALLAS device exposes only the future, not the past. And even the future requires your live fingerprint to access. The breach radius of a single compromise is bounded to a single transaction at worst.
- No archive attack is possible. Even if every XInfinitum transaction ever broadcast were recorded by an adversary today, there is nothing to decrypt retroactively — the signing keys never existed long enough to be captured, and there is no persistent key to recover.
- AI validators sign with the same guarantee. Every validator vote and consensus message uses a Quantum State Key that is generated and destroyed per event. The entire network — not just users — operates under transaction-level forward secrecy.
7.5 Signing Tiers — KYC for Wallets, Biometric for Personhood
KYC identity verification is required for all human wallet creation. Biometric liveness is required for Praemium Program enrollment and DAO governance voting. The core signing security property — ephemeral, quantum-derived, single-use keys — is fully preserved at every tier regardless of biometric requirement.
| Signing Tier | Who | Entropy Source | KYC / Biometric | Use Cases |
|---|---|---|---|---|
| Tier 1 — Hardware | Human with PALLAS QSSK | On-device hardware QRNG (ID Quantique IDQ6MC1) | KYC required for wallet activation · Hardware biometric liveness inside secure element required for Praemium + governance | All transactions · Praemium enrollment · DAO governance voting |
| Tier 2 — Software | Human, software wallet | QRNG API (ID Quantique cloud / ANU QRNG) | KYC required for wallet activation · Device biometric via phone TEE required for Praemium + governance | All standard transactions · Praemium enrollment · DAO governance voting |
| Tier 3 — Programmatic | AI validators, smart contracts, automated signers | QRNG API | None — validators identified by staked position + DAO-approved zkML commitment hash | Block validation votes · Consensus messages · Reward distributions · Contract execution |
7.6 Dilithium5 Signature Size & Block Design
Post-quantum security does not come free of cost. CRYSTALS-Dilithium5 (ML-DSA Level 5) produces significantly larger cryptographic artefacts than classical ECDSA. This has direct implications for block size, transaction data, and network bandwidth — and XInfinitum's design accounts for all of them explicitly.
| Parameter | ECDSA (secp256k1) | CRYSTALS-Dilithium5 (ML-DSA) | Size Ratio |
|---|---|---|---|
| Public key | 33 bytes (compressed) | 2,592 bytes | 79× |
| Signature | 64 bytes | 4,595 bytes | 72× |
| Private key | 32 bytes | 4,896 bytes (ephemeral — destroyed) | 153× |
An average XInfinitum transaction, including sender reference, recipient ZK proof, amount, timestamp, and Dilithium5 signature, is approximately 5.5–6.5 KB — compared to ~250 bytes for a standard Ethereum ERC-20 transfer. This larger transaction size is the direct cost of quantum-resistant security at NIST Level 5.
7.6.1 Block Size Response
XInfinitum targets a 128 MB block size to accommodate Dilithium5 signature overhead while maintaining ~4,000 TPS at mainnet genesis:
| Calculation | Value |
|---|---|
| Target TPS (mainnet, 15 validators) | 4,000 |
| Block time | 2 seconds |
| Transactions per block | 8,000 |
| Average transaction size (with Dilithium5) | ~6 KB |
| Raw block data requirement | ~48 MB |
| Target block size (with overhead + zkML proofs) | 128 MB |
| Sustained network bandwidth (full nodes) | ~512 Mbps peak |
7.6.2 Signature Compression Roadmap
XInfinitum's Phase 3 and Phase 4 roadmap includes two mechanisms to reduce the effective per-transaction signature overhead:
- Dilithium5 batch verification: NIST FIPS 204 supports batch signature verification, where N signatures can be verified simultaneously with sub-linear overhead compared to N individual verifications. This does not reduce signature size on-chain but significantly reduces validator processing time per block.
- zkML ASIC hardware (Phase 4): Custom ASIC hardware for zkML proof generation reduces proof generation time from <30s (GPU) to <2s (ASIC) — enabling faster block times and higher TPS on the same validator infrastructure without increasing block size.
- L2 rollup compression: Layer 2 rollups aggregate thousands of transactions into a single L1 transaction with one aggregated proof — reducing the effective per-transaction signature footprint by orders of magnitude. This is the primary scaling mechanism for XInfinitum beyond the base layer.
8 · Token & Tokenomics
| Parameter | Value |
|---|---|
| Name | XFIN |
| Network | XInfinitum (native L1) |
| Total Supply | 1,000,000,000 XFIN — hard cap, permanently fixed |
| Decimals | 22 |
| Base unit | 1 Quantum = 0.0000000000000000000001 XFIN (10⁻²²) |
| Supply type | Fixed cap with mild deflationary pressure via fee burn (3% of every fee burned) |
8.1 Token Distribution
| Allocation | Amount (XFIN) | % | Notes |
|---|---|---|---|
| Staking & Liquidity Rewards Pool | 400,000,000 | 40% | Distributed over 15 years, declining schedule |
| Grants & Ecosystem Development | 200,000,000 | 20% | DAO-controlled, milestone-gated |
| Founders | 100,000,000 | 10% | 4-year vesting, 1-year cliff, monthly unlock |
| Team Pool | 100,000,000 | 10% | Employee grants, advisors & future hires — unused balance to treasury |
| Treasury (Foundation DAO) | 100,000,000 | 10% | DAO-governed operations, legal, R&D |
| Public Sale — Mainnet Launch | 100,000,000 | 10% | Via XInfinitum Foundation upon mainnet activation (Q1 2028) |
8.2 Token Utility
- Transaction fees (denominated in Quanta for micro-payments)
- AI validator staking (minimum $33,333 USD equivalent in XFIN maintained continuously — Bootstrap Grant Program available for qualifying applicants)
- Storage node staking (to host encrypted token shards)
- DAO governance voting (1 human = 1 vote, PALLAS QSSK biometric verification required)
- Liquidity pool participation and LP token staking
- DeFi protocol participation (lending, borrowing, yield farming on XInfinitum-native protocols)
- Fungible token issuance (deploy custom tokens on the XInfinitum network using the XFIN token standard)
- NFT minting and trading (native NFT standard; XFIN is the settlement currency)
- Access to priority mempool lanes (optional fee premium)
8.3 Public Token Sale Structure
The 10% public sale allocation (100,000,000 XFIN) will be conducted at mainnet genesis in Q1 2028. All public sale participants are subject to the same KYC wallet creation process as all XInfinitum users — no anonymous participation.
| Parameter | Detail |
|---|---|
| Allocation | 100,000,000 XFIN (10% of fixed supply) |
| Sale mechanism | Dutch auction over 7 days — price starts at a ceiling and declines until all tokens are allocated, ensuring fair price discovery without front-running |
| KYC requirement | Mandatory — same ZK-KYC onboarding as wallet creation. Restricted jurisdictions excluded. |
| Minimum purchase | 100 XFIN |
| Maximum purchase per wallet | 500,000 XFIN (~0.05% of supply) — anti-concentration limit |
| Lockup | None — public sale tokens are immediately liquid at mainnet launch |
| Payment currencies accepted | Fiat (CAD, USD via regulated exchange partner) and select PQC-native assets |
| Proceeds allocation | 60% to XInfinitum Foundation Treasury · 30% to Pilon Laboratories operations · 10% to legal/regulatory/audit reserve |
8.3.1 Strategic & Seed Round
Prior to the public sale, Pilon Laboratories will conduct a seed/strategic investment round for accredited investors. This round is separate from the public sale allocation and is funded from the Grants & Ecosystem Development pool (20%) and/or Pilon Laboratories' own founder allocation. Terms are governed by SAFE notes or direct equity in Pilon Laboratories Inc. — not XFIN token pre-sale. Strategic investors receive equity in the operating company, not a token allocation ahead of public participants, preserving fairness of the public token distribution.
Institutional investors interested in XFIN token exposure prior to public sale may contact Pilon Laboratories to discuss structured arrangements subject to applicable securities regulations in their jurisdiction.
9 · Fee Structure
XInfinitum fees are proportional to transaction value — not flat. Transactions of $25 USD or less are fee-free (base gas only) — making XInfinitum the optimal network for micropayments, tipping, and small remittances.
| Component | Rate | Recipient |
|---|---|---|
| Network fee | 0.0025% of USD transaction value | 50% validators · 37% staking & liquidity rewards · 10% treasury · 3% burned |
| Wallet fee | 0.000625% of USD value (25% of network fee) | 100% wallet operator (Pilon Labs / third-party) |
| Base gas | 0.00005 XFIN flat (all transactions) | 50% validators · 37% staking & liquidity rewards · 10% treasury · 3% burned |
| Free tier | Transactions ≤ $25 USD | Percentage fee waived; base gas only |
9.1 Competitive Comparison — $250 Remittance
| Provider | Fee | % of $250 |
|---|---|---|
| Western Union | ~$12.50 | 5.0% |
| Bank wire / SWIFT | ~$25–45 | 10–18% |
| Bitcoin | ~$1.00 | 0.4% |
| XInfinitum | $0.0078 | 0.00313% |
XInfinitum is 1,600× cheaper than Western Union on a $250 remittance. The recipient's family keeps an extra $12.49 per transfer — $149.88/year at one transfer per month.
10 · Staking & Rewards
| Staking Type | Base APY | Lock Period |
|---|---|---|
| Flexible staking | 5.0% | None — withdraw anytime |
| Liquidity pool participation | 7.7% | None |
| LP token staking | 8.0% | None |
| AI Validator staking | 25–40% estimated | 1 year minimum (includes slashing risk) |
The 400M XFIN Staking & Liquidity Rewards Pool is distributed over 15 years on a declining emission schedule. Year 1 effective APY at 40% staked supply: 18–25%. Stated APYs are mature steady-state targets. Validator staking rewards compensate validators for compute costs and slashing risk — they are separate from the Praemium surplus pool.
10.1 Extended Lock Multipliers
Token holders who voluntarily commit to extended lock periods earn a yield multiplier applied to their base staking APY. This rewards long-term network alignment and deepens liquidity stability.
| Lock Period | Multiplier | Flexible (5%) | LP Part. (7.7%) | LP Token (8%) |
|---|---|---|---|---|
| 1 year | 1.3× | 6.5% | 10.0% | 10.4% |
| 1.5 years | 1.6× | 8.0% | 12.3% | 12.8% |
| 2 years | 1.9× | 9.5% | 14.6% | 15.2% |
| 2.5 years | 2.2× | 11.0% | 16.9% | 17.6% |
| 3 years | 2.5× | 12.5% | 19.3% | 20.0% |
Multipliers apply to accumulated rewards only — staked principal is always returnable in full at end of lock period. Early unlock is permitted at any time; however, 50% of accumulated rewards earned to date are forfeited and redistributed to the staking rewards pool. Principal is never at risk from an early exit.
11 · The Xinfinitum Praemium Program
XFIN — The Cryptocurrency That Pays You.
One human. One wallet. One equal share. Every month.
The Xinfinitum Praemium Program is a foundational economic feature made possible exclusively by the AI consensus architecture. After AI validators pay their verified compute costs, everything left over belongs to the network's people — divided equally, every month, automatically.
This program cannot exist on a proof-of-work or proof-of-stake chain. In both models, all surplus revenue flows to miners or stakers in proportion to capital investment. In XInfinitum's AI consensus, validators are software agents whose entire economic requirement is their verified compute cost. Any earnings above those costs represent genuine network surplus with no natural owner — which the Praemium Program distributes equally to every verified human on the network.
11.1 Proof of Personhood
The one-time registration process that qualifies a wallet for the Praemium requires verified unique human identity through one of two methods:
- Tier 1 — PALLAS QSSK Device Enrollment (Automatic): Holders of PALLAS QSSK hardware devices are automatically eligible. The biometric verification is performed on-chip; no biometric data leaves the device. Hardware enforces one-person-one-wallet at the physical layer.
- Tier 2 — KYC Identity Enrollment (Universal Access): Any government-issued ID from any jurisdiction accepted. Free of charge. The KYC service generates a Zero-Knowledge Enrollment Proof — proving "this wallet belongs to a unique verified human" without revealing who. The identity document is permanently deleted after verification. Only a non-reversible nullifier is retained to prevent duplicate enrollment.
11.2 Projected Monthly Distributions
The Praemium is funded exclusively from network surplus — fees collected after AI validators have been compensated for their verified compute costs. AI validator staking rewards are a separate payment to validators and are not included in the Praemium pool. This keeps the Praemium structurally independent: validator economics and human dividend economics cannot cannibalize each other.
| Network Scale | Daily Transactions | Monthly Surplus | Per Address / Month | Per Address / Year |
|---|---|---|---|---|
| Early Stage | 1,000,000 | ~$600 | ~$0.00012 | ~$0.04 |
| Growth Phase | 10,000,000 | ~$8,000 | ~$0.0016 | ~$0.58 |
| Streaming Scale | 100,000,000 | ~$92,000 | ~$0.018 | ~$6.60 |
| Mature Network | 500,000,000 | ~$475,000 | ~$0.095 | ~$34 |
| Full Scale | 1,000,000,000+ | ~$950,000+ | ~$0.19+ | ~$69+ |
Assumes average transaction fee of $0.001 USD and 5,000,000 enrolled addresses.
11.3 Distribution Mathematics — Full Accounting
The Praemium projection table assumes an average transaction fee of $0.001 USD. Here is how that assumption is derived and how the full fee pool is allocated:
Fee derivation: XInfinitum charges 0.0025% of USD transaction value. For the average transaction fee to equal $0.001 USD, the implied average transaction size is:
Full fee pool allocation at 500M daily transactions:
| Pool | Rate | Monthly Amount (500M daily tx) | Recipient |
|---|---|---|---|
| Total fee collected | 100% | ~$15,000,000 | — |
| Validator rewards | 50% | ~$7,500,000 | AI validator operators |
| Staking & liquidity pool | 37% | ~$5,550,000 | XFIN stakers and LP providers |
| Foundation treasury | 10% | ~$1,500,000 | DAO-governed operations |
| Burned (deflationary) | 3% | ~$450,000 equivalent | Permanently removed from supply |
Praemium pool calculation: The Praemium is funded from the validator surplus — the portion of validator rewards remaining after verified compute costs are deducted. Estimated validator compute costs at mature network scale (100 validators × ~$5,000/month average infrastructure):
The projection table uses a conservative estimate of the Praemium pool — specifically the validator surplus only, without staking pool contributions. At DAO discretion, the staking pool surplus contribution could substantially increase per-address distributions beyond the projected figures. The table's "$475,000/month surplus" figure represents the conservative floor at 500M daily transactions, assuming validator compute costs consume a meaningful portion of the validator fee pool.
12 · Governance — The Xinfinitum Foundation DAO
XInfinitum is built by Pilon Laboratories Inc., a private Canadian corporation. Protocol governance is progressively transferred to the Xinfinitum Foundation DAO as network milestones are achieved.
| Phase | Control |
|---|---|
| Phase 1 — Testnet | Pilon Labs holds full protocol control |
| Phase 2 — Mainnet | DAO controls validator admission and treasury |
| Phase 3 — Growth | DAO controls protocol parameters and upgrades |
| Phase 4 — Maturity | Full DAO governance; Pilon Labs = service provider only |
12.1 DAO Participation
DAO governance requires: (1) minimum staked XFIN equivalent to $10,000 USD (dynamic floor); (2) registered PALLAS QSSK device with biometric verification at time of voting; (3) on-chain biometric commitment. Every qualifying participant receives exactly 1 vote regardless of stake amount — wealth buys more yield, not more governance influence.
12.2 Proposal Thresholds
| Proposal Type | Fee | Quorum | Approval |
|---|---|---|---|
| Parameter adjustment | $50 USD equiv. in XFIN | 5% | 60% |
| AI model training approval | $75 USD equiv. in XFIN | 7% | 66% |
| Protocol upgrade | $120 USD equiv. in XFIN | 10% | 75% |
| Constitutional amendment | $150 USD equiv. in XFIN | 20% | 80% |
13 · Security Model & Post-Quantum Cryptography
| Function | Algorithm | Standard |
|---|---|---|
| Transaction signatures | CRYSTALS-Dilithium5 (ML-DSA) | NIST FIPS 204 · Level 5 |
| Key encapsulation | CRYSTALS-Kyber (ML-KEM) | NIST FIPS 203 |
| Token storage encryption | CRYSTALS-Kyber + AES-256-GCM | NIST FIPS 197 |
| Shard distribution | Shamir Secret Sharing (3-of-5) + decoy shards | Information-theoretic security |
| zkML proofs | PLONK universal proof system | ZK-SNARK |
| Entropy source | QRNG — ID Quantique Quantis / ANU API | NIST SP 800-90B |
| Hashing | SHA3-256, SHA3-512 | NIST FIPS 202 |
| Key derivation | HKDF-SHA3-512 | RFC 5869 |
13.1 Perpetual Token Encryption Architecture
XInfinitum tokens are never stored in plaintext anywhere on the network at any time. Every XFIN token in existence undergoes the following lifecycle immediately upon issuance and remains in this state permanently:
- Compression: Token data is compressed before encryption to reduce shard size and network overhead.
- Encryption: Each token is individually encrypted using CRYSTALS-Kyber key encapsulation + AES-256-GCM symmetric encryption. The encryption key is itself derived from network consensus entropy — no single party holds it.
- Sharding: The encrypted token is split into shards using Shamir Secret Sharing (3-of-5). Any 3 shards can reconstruct the token; 2 or fewer shards reveal nothing.
- Decoy shard injection: For every real shard distributed to the network, additional cryptographically indistinguishable decoy shards are distributed alongside it. An adversary observing shard traffic cannot distinguish real shards from decoys, making targeted shard theft structurally ineffective.
- Distribution: Real and decoy shards are distributed across geographically diverse storage nodes. No single node holds a complete token or enough real shards to reconstruct one.
Tokens never leave this encrypted, sharded state. They are not "decrypted and transferred" during a transaction. Instead, XInfinitum maintains a cryptographically secured ledger of claims — ownership records that attest which wallet controls which token allocation. When a transaction occurs, the ledger updates the claim. The underlying encrypted token shards do not move; only the on-chain ownership record changes.
13.2 Mempool Privacy Architecture
A blockchain mempool — the waiting room where unconfirmed transactions are held before inclusion in a block — is a significant attack surface on classical chains. On Ethereum and Bitcoin, the entire mempool is public. Validators (miners) can see destination addresses, amounts, and timing for all pending transactions. This enables front-running, MEV (maximal extractable value) extraction, and targeted address surveillance. XInfinitum addresses all three at the protocol level.
Private destination addresses in the mempool: When a sender submits a transaction to the XInfinitum mempool, the recipient address is not included in plaintext. Instead, the sender includes a one-time stealth address derived from the recipient's public spend key using Diffie-Hellman key exchange on a post-quantum curve. Only the intended recipient — who holds the corresponding private spend key — can recognize that the stealth address belongs to them. Validators process and include the transaction without knowing who the recipient is. The recipient's wallet scans incoming blocks and identifies transactions directed to them by performing the same derivation locally.
Dandelion++ transaction propagation: XInfinitum uses Dandelion++ for all transaction broadcasting. In a standard gossip network, a transaction is broadcast simultaneously to all peers — making it trivial to identify the originating node (and by extension, the sender's IP address) by timing analysis. Dandelion++ first routes the transaction through a random "stem" path (a single random relay chain) before entering "fluff" phase (standard broadcast). This anonymizes the origin node by making timing analysis statistically unreliable. Combined with the stealth address, a passive network observer cannot link a transaction to either the sender's IP or the recipient's wallet address.
ZK proof of valid destination: Because destination addresses are private in the mempool, validators cannot verify that the recipient address is a valid, registered XInfinitum wallet from the plaintext alone. XInfinitum solves this with a zero-knowledge proof attached to each transaction — a succinct PLONK proof that attests: "This stealth address corresponds to a registered, valid wallet, and the sender's claim balance is sufficient to cover this transaction amount" — without revealing either the recipient's identity or the sender's full balance. Validators verify the proof (fast, ~5ms) and include the transaction without ever learning the recipient's on-chain identity.
| Threat | XInfinitum Countermeasure |
|---|---|
| Front-running / MEV extraction | Encrypted destination + stealth addresses — validators cannot see recipient to reorder profitably |
| Address surveillance | One-time stealth address per transaction — no two transactions point to the same visible address |
| Network-level IP deanonymization | Dandelion++ stem phase obscures the originating node from timing analysis |
| Transaction linkage | Stealth address unlinkability — external observers cannot link sender + recipient across transactions |
| Invalid destination spam | ZK proof of valid destination — validators reject transactions without a valid proof; no lookup table exposed |
13.3 Network Fork Policy & Safety Guarantees
XInfinitum's BFT consensus (Tendermint-based) provides a fundamentally different safety model than proof-of-work chains. Bitcoin's safety is probabilistic — a transaction is "final" only in a statistical sense after 6+ blocks, because a fork can theoretically still replace it. XInfinitum provides mathematical, single-block finality: once a block is committed by a supermajority (≥⅔ + 1 of validators), it cannot be reversed under any conditions that don't simultaneously require controlling ≥⅓ of all voting power.
Fork freedom guarantee: In Tendermint BFT, two conflicting blocks at the same height can only both achieve commit status if ≥⅓ of validators sign both — which constitutes provable double-signing and triggers automatic slashing. A fork requires either: (a) ≥⅓ of validators to commit slashable equivocation, permanently destroying their staked capital; or (b) a network partition where both sides believe the other is offline. Case (a) is economically irrational and immediately punished on-chain. Case (b) is handled by the safety-over-liveness rule described below.
Safety over liveness — partition behavior: When the network detects that consensus cannot be achieved (validator quorum unreachable — e.g. due to a network partition), XInfinitum halts block production rather than allowing either partition to continue independently. This is the "safety over liveness" choice in the CAP theorem: XInfinitum guarantees consistency (no conflicting chain heads) at the cost of availability during a partition. Once the partition heals and ≥⅔ + 1 of validators can communicate, block production resumes automatically from the last committed block. No manual intervention or chain rollback is required.
Validator set changes and governance forks: Protocol upgrades that require validator software changes follow a two-phase governance process: (1) DAO proposal passes with ≥75% approval and 10% quorum; (2) validators have a mandatory 14-day upgrade window before the switchover block height. If fewer than ⅔ of validators have upgraded by the switchover block, the upgrade is automatically postponed by 7-day increments until quorum is achieved. This eliminates "contentious hard fork" scenarios — an upgrade either achieves supermajority adoption or it doesn't proceed.
14 · Network Phases & Roadmap
| Phase | Target | Key Milestones |
|---|---|---|
| Phase 1 — Testnet | Q2 2027 | 7 AI validators · zkML proof system · PALLAS QSSK wallet integration · KYC onboarding system · Praemium enrollment testing · PQC bridge framework · Software QRNG mode |
| Phase 2 — Mainnet Genesis | Q1 2028 | 15 validators · Public token launch · Praemium Program live · DAO treasury control · XFIN exchange listings · XInfinitum Foundation incorporated (Cayman Islands) |
| Phase 3 — Growth | 2029 | 51 validators · EVM compatibility layer · DEX launch · XInfinitum Card Program · XFINUSD stablecoin launch · XFIN perpetuals market · First DAO-approved PQC-chain native bridges |
| Phase 4 — Maturity | 2030+ | 100+ validators · Full DAO governance · L2 rollup support · .xinfinitum domain service · zkML ASIC hardware · XFINCAD stablecoin · Expanded PQC-native multi-chain bridge ecosystem |
15 · Planned Protocol Extensions
15.1 XFINUSD & XFINCAD — Delta-Neutral Stablecoins
XInfinitum plans to launch two native delta-neutral stablecoins in Phase 3: XFINUSD (pegged to the US Dollar) and XFINCAD (pegged to the Canadian Dollar). Unlike centralized stablecoins such as USDC or USDT — which require trust in a bank custodian and are subject to account freezes, debanking risk, and regulatory seizure — XInfinitum stablecoins are maintained entirely on-chain through a hedged collateral mechanism.
15.1.1 How Delta-Neutral Pegging Works
A delta-neutral stablecoin holds a hedged position that cancels out price exposure to the underlying collateral:
- User deposits XFIN as collateral into the stablecoin protocol smart contract.
- The protocol simultaneously opens a short position on an equivalent XFIN value via the XInfinitum perpetuals market — cancelling out price exposure. Whether XFIN rises or falls, the combined position holds its USD or CAD value.
- XFINUSD or XFINCAD is minted to the user in the equivalent pegged amount.
- Redemption reverses the process — stablecoin is burned, short is closed, XFIN collateral is returned.
This model was pioneered at scale by Ethena Protocol (USDe), which grew to over $5B in circulation using the same mechanism with Ethereum as collateral. XInfinitum's implementation uses XFIN as collateral and targets both USD and CAD pegs.
15.1.2 Why XFINCAD Is Strategically Significant
No major blockchain currently has a widely adopted, natively issued CAD-pegged stablecoin. XFINCAD would be the first serious Canadian-dollar stablecoin on a purpose-built Layer 1 — directly aligned with Pilon Laboratories' Canadian origin, and positioned to attract Canadian institutional participants, remittance corridors, and regulated financial services that require CAD settlement. CADC (the existing CAD stablecoin) has minimal adoption and no native blockchain — XFINCAD fills this gap entirely.
15.1.3 Prerequisites & Sequencing
Delta-neutral stablecoins require underlying infrastructure that does not exist at mainnet genesis. Launch is contingent on:
- XFIN listed on exchanges with sufficient trading volume to support hedging at scale
- XInfinitum-native perpetuals market operational (Phase 3 DEX launch)
- Chainlink or equivalent oracle providing real-time XFIN/USD and XFIN/CAD price feeds
- Reserve fund established to absorb periods of negative funding rates
- Full smart contract audit by an independent security firm
15.1.4 Stablecoin Revenue Model
The stablecoin protocol generates revenue from minting and redemption fees (0.1–0.3%) and positive funding rate income from the short position during bullish market conditions. This revenue flows to the Foundation Treasury and ultimately contributes to the Praemium surplus pool — adding a third income stream to the universal dividend alongside network fees and validator surplus.
15.2 XInfinitum Card Program
The XInfinitum Card Program will allow XFIN holders to spend their tokens at any merchant accepting Visa or Mastercard worldwide — converting XFIN to the local fiat currency at point of sale. Cards are issued through a licensed financial institution partner on the Visa and Mastercard networks.
| Card Type | Fee | Features |
|---|---|---|
| Virtual Card | $9.00 CAD / year | Instant issuance · Online payments · Apple Pay / Google Pay compatible |
| Physical Card | $22.00 CAD one-time | Tap-to-pay NFC · Worldwide acceptance · Apple Pay / Google Pay compatible |
Both card types are funded directly from the cardholder's XInfinitum wallet. Conversion from XFIN to fiat occurs at the moment of transaction using the live market rate. Card credentials are stored in the user's encrypted wallet vault and can be added to Apple Pay or Google Pay for contactless payments.
15.2.1 PALLAS QSSK — NFC Payment Integration
The PALLAS QSSK hardware device is designed with an NFC module, enabling it to function as a contactless payment device at any NFC-enabled terminal. The PALLAS companion app allows users to load credit cards, debit cards, and their XInfinitum Card directly into the device's encrypted vault. Payment is triggered by the biometric fingerprint sensor — the same liveness-verified touch that authorizes all other device functions. No card number is transmitted in plaintext; credentials are tokenized inside the secure element before transmission, matching the security model of Apple Pay.
This makes the PALLAS QSSK a complete physical wallet replacement — a single device that serves as a post-quantum security key, hardware cryptocurrency wallet, encrypted identity vault, and NFC payment terminal, all protected by biometric liveness detection and quantum-resistant cryptography.
16 · Revenue Model & Network Economics
XInfinitum generates protocol revenue through five independent streams. These streams are structurally separate — no single stream's performance affects the others, and each feeds into distinct network pools (validator rewards, treasury, Praemium, burn).
16.1 Network Transaction Fees
The primary revenue source is the proportional network fee (0.0025% of USD transaction value) collected on every transaction above $25 USD. At mature network scale of 500M daily transactions, this generates approximately $475,000 USD in monthly fee revenue before validator cost deduction. The Praemium surplus is the portion remaining after validators are compensated.
16.2 Address Shortening Service — .xfin Domains
XInfinitum wallet addresses are 64-character hexadecimal strings by default. The Address Shortening Service allows users to register a human-readable short address (e.g. derek.xfin) that resolves to their full wallet address — functioning identically to ENS (Ethereum Name Service) on Ethereum.
| Tier | Annual Fee | Description |
|---|---|---|
| Standard address (5+ characters) | $7.00 USD/year | e.g. derek.xfin, alice.xfin |
| Short address (3–4 characters) | $35.00 USD/year | e.g. ace.xfin, zk.xfin — premium for brevity |
| Single character (1–2 characters) | $200.00 USD/year | Reserved for auction; high-demand identifiers |
Annual fees are paid in XFIN at USD-equivalent market rate. 80% of registration revenue flows to the Foundation Treasury; 20% is burned, contributing to XFIN's deflationary pressure. At 1,000,000 registered addresses at an average of $8/year, this stream generates $8M USD/year in treasury revenue.
16.3 Wallet Fee Revenue
The PALLAS Wallet App and any third-party wallets built on XInfinitum collect a wallet fee of 0.000625% of transaction value (25% of the base network fee). This revenue stream accrues entirely to the wallet operator — for Pilon Laboratories' own PALLAS Wallet App, this is direct company revenue separate from the protocol treasury.
16.4 XInfinitum Card Program Fees
Virtual Card ($9 CAD/year) and Physical Card ($22 CAD one-time) issuance fees provide recurring and one-time revenue. At 100,000 cardholders, this generates approximately $900,000 CAD/year in virtual card renewals plus one-time physical card revenue.
16.5 Stablecoin Protocol Fees (Phase 3+)
Minting and redemption fees (0.1–0.3%) on XFINUSD and XFINCAD stablecoin operations contribute to the Foundation Treasury once the perpetuals market and stablecoin protocol are live in Phase 3. At $100M circulating stablecoin supply with 10% monthly turnover, this contributes approximately $1–3M/month to treasury revenue.
16.6 Projected Revenue Summary
| Stream | Phase 2 (2028) | Phase 3 (2029) | Phase 4 (2030+) |
|---|---|---|---|
| Network transaction fees (treasury 10%) | ~$50K/mo | ~$500K/mo | ~$5M+/mo |
| .xfin address registrations | — | ~$100K/mo | ~$700K+/mo |
| PALLAS Wallet App fees | ~$20K/mo | ~$200K/mo | ~$2M+/mo |
| XInfinitum Card fees | — | ~$75K/mo | ~$300K+/mo |
| Stablecoin protocol fees | — | ~$250K/mo | ~$3M+/mo |
Revenue figures are forward-looking estimates based on comparable network growth trajectories and do not constitute a guarantee of future performance. All figures in USD equivalent.
17 · PALLAS QSSK — Quantum State Security Key Hardware Device
The PALLAS QSSK hardware device is the physical embodiment of the Quantum State Key protocol. Manufactured by Pilon Laboratories Inc. under the PALLAS product line, it provides the highest security tier for XInfinitum wallet operations and serves as the hardware Proof-of-Personhood credential for DAO governance and Praemium enrollment.
- Embedded QRNG: ID Quantique IDQ6MC1 — certified quantum entropy, physically non-deterministic
- Secure Element: Infineon SLE97 · Common Criteria EAL 6+ — all key operations inside the SE, never exported
- Biometric sensor: Synaptics FS7600 · Hardware liveness detection — single biometric = single governance identity
- Signature algorithm: CRYSTALS-Dilithium5 (NIST FIPS 204) — quantum-resistant at Level 5
- Multi-function: XInfinitum hardware wallet · FIDO2 security key · Encrypted data vault
18 · Storage Node Network
Storage nodes are a dedicated class of XInfinitum network participant responsible for storing the encrypted token shards that make up the Perpetual Token Encryption Architecture (Section 13.1). They are distinct from AI validators — validators achieve consensus and produce blocks; storage nodes persist the encrypted shard data that the blockchain's ownership ledger points to. Both roles are essential and separately compensated.
18.1 Storage Node Requirements
| Requirement | Specification | Notes |
|---|---|---|
| Minimum stake | 5,000 XFIN (held continuously) | Slashed on provable data unavailability or tampering. Stake acts as collateral guaranteeing data integrity. |
| Storage hardware | 4 TB+ NVMe SSD (minimum); 16 TB+ recommended | Encrypted shard data grows with network usage. Storage capacity determines shard assignment ceiling. |
| Memory | 16 GB RAM minimum · 32 GB recommended | Required for efficient shard serving and proof generation under load. |
| Network | 100 Mbps symmetric · low latency (<50ms to nearest validator region) | Storage nodes must serve shard requests during transaction processing windows. High latency causes missed serving windows and reduced rewards. |
| Uptime SLA | 99.5% (measured monthly) | Nodes falling below 99.5% uptime in any 30-day window are penalized by reduced reward weight. Nodes below 95% for 7 consecutive days enter an automatic cooldown and lose shard assignments. |
| Software | XInfinitum Storage Node Client (open source) | Runs as a background service; supports Linux, Windows Server, macOS. No GPU required. |
18.2 Shard Assignment & Redundancy
Each encrypted token is sharded into 5 pieces using Shamir Secret Sharing (3-of-5 threshold). Real shards and decoy shards are assigned to storage nodes by the protocol using a deterministic but unpredictable assignment function derived from the block hash at the time of shard creation. No storage node is informed which of the shards it holds are real versus decoy — this is a structural privacy guarantee.
The protocol maintains a minimum of 3× geographic redundancy for each real shard — meaning the same real shard is held by at least 3 storage nodes in at least 2 different continental regions. This redundancy is continuously verified by the validator network via probabilistic shard availability proofs. If a node fails to produce a valid availability proof when challenged, it is flagged and its shard assignments redistributed within one consensus round.
18.3 Storage Node Compensation
Storage nodes are compensated from two sources: a share of the network fee allocation, and a dedicated storage subsidy funded from the Foundation Treasury during the network's early growth phase when transaction volume is still building.
| Compensation Component | Rate / Mechanism | Phase |
|---|---|---|
| Network fee share | Storage nodes collectively receive 5% of total network fees, distributed proportionally by verified storage capacity and uptime score | All phases |
| Foundation storage subsidy | Fixed monthly XFIN grant from Treasury — declining schedule over 4 years as transaction fee revenue scales to cover storage costs organically | Phase 2–3 (tapering) |
| Uptime performance bonus | Nodes maintaining 99.9%+ uptime for 90 consecutive days receive a 1.25× reward multiplier for that quarter | All phases |
| Shard serving fees | Micro-fee paid per shard served during transaction reconstruction — paid by the transacting wallets as part of base gas | Phase 3+ |
Storage nodes do not require GPU hardware and have significantly lower capital requirements than AI validator nodes. The 5,000 XFIN staking requirement and commodity hardware specifications are intentional — XInfinitum's storage layer is designed to be run by individuals, not exclusively by data centres, preserving geographic decentralization of the shard network.
18.4 Becoming a Storage Node Operator
Storage node registration opens during Phase 1 (Testnet, Q2 2027). Operators submit a node registration transaction staking their 5,000 XFIN, declare their storage capacity and geographic region, and install the XInfinitum Storage Node Client. The protocol assigns initial shard responsibilities within one epoch of registration. A Bootstrap Grant Program (mirroring the AI Validator Bootstrap Grant) will be available for qualifying operators who demonstrate adequate hardware but lack sufficient XFIN to meet the staking requirement at genesis.
19 · References
The following papers, standards, and protocols form the technical foundation of the XInfinitum design. Where a referenced work has been updated or superseded, the most current version cited here was current as of the whitepaper revision date.
19.1 Consensus & BFT
- Buchman, E., Kwon, J., & Milosevic, Z. (2018). The latest gossip on BFT consensus. arXiv:1807.04938. — Tendermint BFT consensus protocol, the formal basis for XInfinitum's consensus layer.
- Castro, M. & Liskov, B. (1999). Practical Byzantine Fault Tolerance. OSDI '99. — Original PBFT paper establishing BFT foundations.
- Fischer, M. J., Lynch, N. A., & Paterson, M. S. (1985). Impossibility of Distributed Consensus with One Faulty Process. JACM 32(2). — FLP impossibility theorem establishing the fundamental liveness/safety tradeoff.
19.2 Post-Quantum Cryptography
- NIST FIPS 203 (2024). Module-Lattice-Based Key-Encapsulation Mechanism Standard (ML-KEM / CRYSTALS-Kyber). National Institute of Standards and Technology. — Key encapsulation standard used for token encryption and key derivation.
- NIST FIPS 204 (2024). Module-Lattice-Based Digital Signature Standard (ML-DSA / CRYSTALS-Dilithium). National Institute of Standards and Technology. — Digital signature standard used for all XInfinitum transaction signing (Dilithium5, Level 5).
- NIST FIPS 205 (2024). Stateless Hash-Based Digital Signature Standard (SLH-DSA / SPHINCS+). National Institute of Standards and Technology. — Hash-based signature fallback standard.
- NIST FIPS 206 (2024). Module-Lattice-Based Key-Encapsulation Mechanism Standard (FN-DSA / FALCON). National Institute of Standards and Technology. — Compact lattice signature standard.
- NIST SP 800-90B (2018). Recommendation for the Entropy Sources Used for Random Bit Generation. NIST. — Standard governing QRNG entropy source certification (ID Quantique IDQ6MC1 compliance reference).
- Shor, P. W. (1994). Algorithms for Quantum Computation: Discrete Logarithms and Factoring. FOCS '94. — Mathematical basis for quantum vulnerability of ECDSA and RSA.
19.3 Zero-Knowledge Proofs
- Gabizon, A., Williamson, Z. J., & Ciobotaru, O. (2019). PLONK: Permutations over Lagrange-bases for Oecumenical Noninteractive arguments of Knowledge. IACR ePrint 2019/953. — Universal ZK-SNARK proof system used for zkML proofs, transaction validity proofs, and ZK-KYC enrollment proofs.
- Groth, J. (2016). On the Size of Pairing-based Non-interactive Arguments. EUROCRYPT 2016. — Groth16 proof system; reference for proof size optimization comparisons.
19.4 Network Privacy
- Fanti, G., Venkatakrishnan, S. B., Bakshi, S., Bhatt, B., Bhatt, S., Pâris, M., & Viswanath, P. (2018). Dandelion++: Lightweight Cryptocurrency Networking with Formal Anonymity Guarantees. Proc. ACM Meas. Anal. Comput. Syst. 2(2). — Dandelion++ transaction propagation protocol used for IP-level anonymization of transaction origin.
- Noether, S. (2015). Ring Signature Confidential Transactions for Monero. IACR ePrint 2015/1098. — Reference for stealth address design and one-time address derivation concepts adapted for XInfinitum's mempool privacy.
19.5 Secret Sharing & Key Management
- Shamir, A. (1979). How to Share a Secret. CACM 22(11). — Shamir Secret Sharing (3-of-5), used for encrypted token shard distribution across storage nodes.
- Krawczyk, H. & Eronen, P. (2010). HMAC-based Extract-and-Expand Key Derivation Function (HKDF). RFC 5869. IETF. — Key derivation function (HKDF-SHA3-512) used for session key and shard encryption key derivation.
19.6 Hardware & Entropy
- ID Quantique. (2023). IDQ6MC1 Quantum Random Number Generator — Datasheet v2.1. ID Quantique SA, Geneva. — QRNG module specification for the embedded hardware entropy source in the PALLAS QSSK device.
- Australian National University (ANU) Quantum Optics Group. ANU QRNG — Real-time quantum random numbers. qrng.anu.edu.au. — Software-mode entropy API used when hardware QRNG is not present (testnet and software wallet fallback).
- Infineon Technologies. (2022). SLE97 Security Controller — Product Brief. Infineon Technologies AG. — Secure element specification (Common Criteria EAL 6+) for the PALLAS QSSK device.
19.7 Protocol Inspirations & Comparable Works
- Kwon, J. & Buchman, E. (2016). Cosmos: A Network of Distributed Ledgers. cosmos.network/whitepaper. — Tendermint consensus reference implementation context.
- Guy, T. & Diamandis, N. (2023). Ethena: Delta-Neutral Synthetic Dollar Protocol. ethena.fi/Ethena.pdf. — Delta-neutral stablecoin mechanism reference (Ethena USDe) for the XFINUSD / XFINCAD design in Section 15.1.
- Buterin, V. (2013). Ethereum White Paper. ethereum.org. — Smart contract platform reference for EVM compatibility layer and ERC-20/ERC-721 equivalents planned in Phase 3.
- Nakamoto, S. (2008). Bitcoin: A Peer-to-Peer Electronic Cash System. bitcoin.org. — Original Bitcoin paper; referenced in Section 4.5 finality comparison (probabilistic vs. mathematical finality).
This whitepaper is a living document. References will be updated as standards are finalized and new peer-reviewed work is published. The most current version of this document is always available at pilonlaboratories.com/xinfinitum.html. Whitepaper version: v2.3. Last revised: May 2026.